The TickTrader Trader’s Room software package
is delivered with ready-to-use integrations with the most requested
trading platforms on the market – MetaTrader 4, MetaTrader 5, and
TickTrader Trading Platform. Take advantage of 60+ fiat payment systems and a digital asset processing service integrated with 20+ blockchains, available from day one of the launch to handle Forex and blockchain operations. Our Forex CRM allows you to access all your client data whenever you need to.
- We take pride in announcing that we have a proven track record of helping brokers with all the technology they need to set up and operate highly efficient brokerages.
- Forex CRM solutions help brokers keep track of potential customers and assign responsible managers to contact them with all necessary trade information.
- Please pay attention that we don’t provide financial services on behalf of B2Broker LTD.
- When it comes to finding the best CRM system for your foreign exchange business, it can be helpful to request estimates from a variety of different vendors.
- Integrations with Scorechain and Bitfury’s Crystal allow blockchain-processed payments to be analyzed for illegal activity.
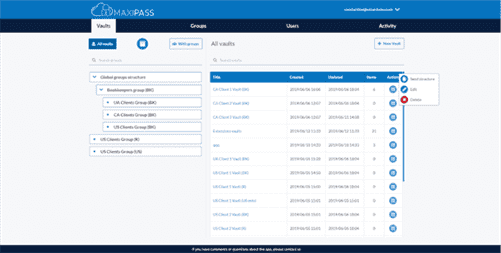
With this knowledge, you can decide which CRM system is right for your business. Trader’s Room is a unifying power that provides you clear monitoring of money flows —
every financial service and every payment system connected in a single Forex platform back office interface. Once connected, you get a fully controlled system that allows you to securely receive
end-user funds, as well as provide you detailed reports and analytics, and much more. Trader’s Room specifically designed for
brokers and companies that need a multifunctional tool to manage massive
flows of funds from clients. If necessary, the Trader’s Room software
infrastructure can be hosted in multiple data centers, including backup servers,
for enhanced fault tolerance.
Trader’s Room:
Brokers should find a deal with providers; the cost will depend on the range of needs required for your company. In this video, B2Core Product Manager, Ivan Navodnyy, talks about one of B2Broker’s flagship products, B2Core. Ivan explores how this industry-leading CRM/traders room solution embraces a huge range of capabilities to offer a unique, customisable service for clients that can be easily tailored to fit each type of organisation. Due to the high functionality of the program, all purchase orders are displayed in one place and have the possibility of additional filtering for each of the specified parameters.

With this software, clients can publish verification papers and create trading accounts. Additionally, the personal office provides customers with a secure place to manage their finances. The admin area is the most essential component in the structure since it controls, organizes, and structures comprehensive information about customer activity, including trade data, its type, duration, etc. This area allows the view of detailed statistics and reports on various criteria and parameters.
A comprehensive guide on forex back office software
Moreover, XCritical back-office platform has a full-fledged ability that helps to make individual settings and provide the necessary access rights to each specific department and employee of your office. For example, Broker 1 can administer account A and simultaneously have limited access to view info on a group of customers B. However, both brokers do not have the ability to manage such parameters in a group like liquidity and other specific functions. During registration, the purchaser must leave such data as e-mail address, phone number, and various identification documents. Also, the integrated program allows you to most effectively keep in touch with the client and track all transactions. That is why it is so essential that each of the departments in a brokerage company has secure access to this privacy policy info for the most efficient use and achievement of common goals.

This section is a combination of various flexible settings for connecting third-party services and applications. Other systems that can be connected to the Forex back office include various trading platforms, “KYC” service providers, rate providers, and various marketing services that help set up an advertising campaign. In general, back office software solutions https://www.xcritical.com/ have evolved with the advent of cloud-based software as a service (SaaS). With back-office software, brokers can extract actionable intelligence from the system without any particular expertise. Back office software for forex brokers should have simple reporting tools so that you can access data about the actions of clients, partners, and other administrators.
What You Need to Know About Forex Back Office Software
CRM trading platforms are the place where all the client’s financial data is stored. Back office forex software should include marketing tools that you and your IBs can both use. With the data from your reports, you should be able to see which clients are actively making trades and which ones have reduced their trading activity. Over the past few years, the crypto space has been developing at lightning speed, being the foundation for creating new branches of development and improvement of blockchain technology. Forex brokerage back office software can work independently of the trading platform your firm uses.
Usually, traders have many back office-related questions and here we assist in that. One of the most significant barriers to clients depositing money is a complicated or lengthy process for funding their accounts. Connecting your back office software to external payment systems (like credit card processors, crypto-currency wallets, and bank transfers) reduces the length of time it takes for deposits to be credited to client accounts. Forex trader’s room provides a hassle-free trading experience with an array of essential and supplementary resources to make the process more convenient. However, Account creation, record maintenance, funding deposits & withdrawals are offered 24/7 for added flexibility in foreign exchange operations. If you’re looking for reliable and powerful FX broker software, B2Core is the perfect solution.
Basics to Know About Forex Back Office Software
Your forex firm’s back office software needs to include a KYC module for enforcing compliance procedures. Look for software that lets you specify an expiration date so you know when new documentation is needed. Back office forex software should make it easy to store and maintain clients’ information forex back office software and personal data. You should be able to create a new client profile quickly and make updates to it without much hassle. Back office technologies support complex data management solutions and processes while allowing companies to spend as fewer as possible and maximize efficiency.
Also, This advanced system can easily handle payments and settlements without extensive investments. Achieving success in foreign exchange requires an effective Forex back office provider. Also, Taking advantage of such a system’s capacity to transform prospects into profitable sales is integral for realizing long-term goals. You need to know what to look for while choosing the right provider for your brokerage.